The Challenges of Exchange Migration
To upgrade or not to upgrade…
System upgrades, whether we like them or not, are a necessary part of our technological world. However, in an effort to save costs, many organizations hold back from rolling out new technology. When upgrade approval finally happens, multiple complex systems are also in the upgrade. Multiple upgrades increase the risk of complicating the execution or lost user productivity because of delays, or at worst - the loss of critical data during the migration process. This post follows the story of an organization that unwillingly upgraded too many IT assets at once because they did not have the resources to keep up with regular maintenance projects.
A challenging migration
A large product and service organization with multiple international offices took on an Exchange 2010 migration project that would affect all of its locations. The migration scope was 20 offices, three network domains, and over 6,000 user mailboxes. The migration also included: Blackberry® Enterprise Server (BES), Outlook Web Access (OWA) services, and the introduction of Microsoft® Forefront® servers to the infrastructure.
The biggest challenge in planning the project was a delay in Windows® Server Domain Active Directory (AD) consolidation that had been in progress for almost a year. Because the business was quickly expanding, many of the satellite offices had set up their own domains with only a trust relationship with the domain of the business headquarters. Due to this, users in those satellite offices were unable to log into the headquarters domain and access corporate resources, even when those users had access rights.
More shortcuts = more risk
Over the years, users followed shortcuts to get user access to the corporate business systems. Some of these quick fixes increased the complexity of user accounts and even introduced IT security risks. In one example, a satellite office was constantly having access issues but rarely with IT resources to resolve the issues. Frustration grew with the office manager that he took matters into his own hands and ordered a second Internet line to the office; setting up a connection with the company’s headquarters and remote controlling a computer to access the organization’s CRM system.
At great risk, the low encryption connection was accessing the Internet from the satellite office and re-entering the organization through an unused network port. When the IT security department found the unauthorized connection, it was shut down immediately and again, this satellite office was without business system resources and had to reopen the original job ticket with IT.
Due to these undocumented fixes the IT engineer working on the AD design wanted to start over and rebuild the systems from the ground up. Unfortunately, with the number of user accounts and dependencies the organization had within its network, a complete reconstruction was not an option.
What happened?
The IT department started a systematic collection of all of the server systems in each office and began documenting an upgrade process that would complete the AD move and lay the foundation for the Exchange 2010 migration. The impacts were larger than originally estimated and the entire project took 18 months - six months longer than planned.
One of the more intricate migrations was for the BES system. There were not enough resources to perform the migration for the entire employee population and as a result, specific instructions were written for users to manually complete the mailbox update on their mobile phones.
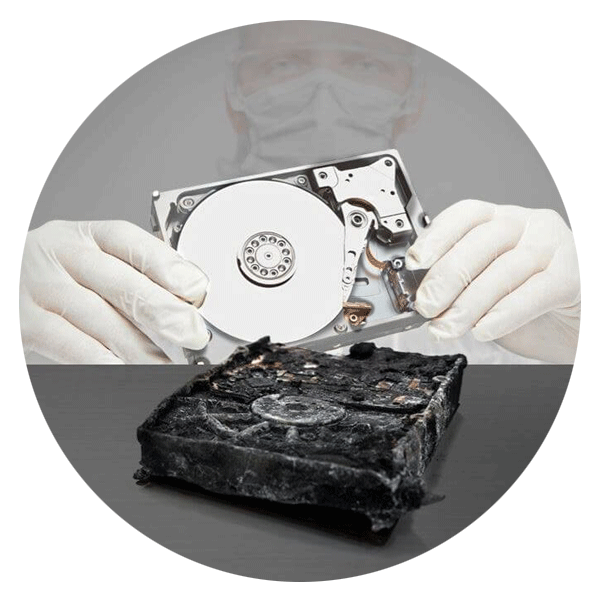
If the process was not performed exactly as written, the BES mailbox synchronization process would work in reverse and all of the user’s archived email data would be lost. Inevitably, some users lost data but fortunately, prior to the upgrade, the IT department’s business continuity plan accommodated for user error and multiple backups were completed at various stages in an effort to minimize data loss.
Was it successful?
This organization used Ontrack PowerControls for Exchange to extract user mailboxes and copy them during the test migration process. Additionally, it was utilized to quickly access archived tape media that contained Information Stores, to extract messages from backups for those users who had not followed the BES migration instructions.
This project was long and tedious, and it required diligence and patience to work through all of the phases and milestones. Yet with savvy IT staff and the use of additional tools to get the job done, this migration was a success.
Call for Immediate Assistance!
- Crypto Currency (2)
- Data Backup (9)
- Data Erasure (8)
- Data Loss (15)
- Data Protection (11)
- Data Recovery (22)
- Data Recovery Software (2)
- Data Security (3)
- Data Storage (15)
- Degaussing (1)
- Deleted Data (5)
- Digital Photo (2)
- Disaster Recovery (6)
- Encryption (1)
- Expert Articles (5)
- Hard Drive (7)
- Laptop/Desktop (7)
- Memory Card (5)
- Mobile Device (13)
- Ontrack PowerControls (1)
- Raid (5)
- Ransomware & Cyber Incident Response (6)
- Server (6)
- SSD (14)
- Tape (17)
- Virtual Environment (9)
