Data Erasure | Production Environment | Ontrack blog
How to Erase Data From a Live Running Server
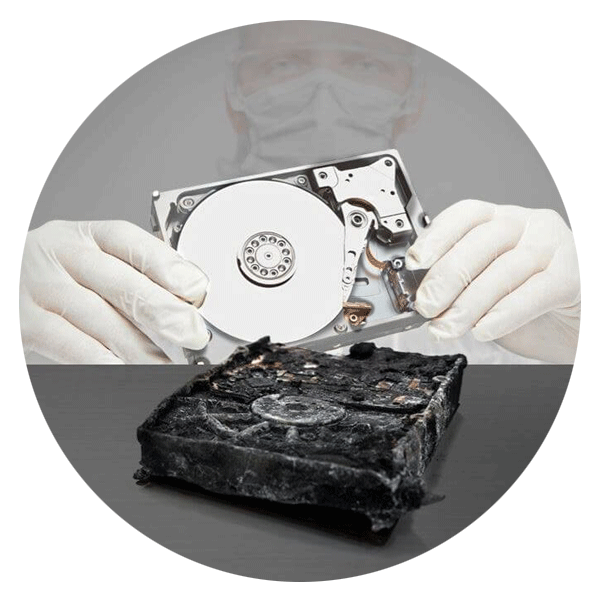
Securely erasing data is definitely not an easy task. Whether it's a single hard disk drive, an SSD in a laptop or a number of enterprise-class storage devices in a live server – pressing the delete button on the keyboard just won´t cut it. As we have pointed out in previous blog posts, using the “Recycle Bin” when it comes to deleting a file is not enough. The same is true with using the “format” command. Deleting data this way is not secure, since only a reference to the file is deleted, not the file itself. What you're essentially doing is deleting a kind of catalog entry linking towards the file. Therefore the file can be restored quite easily using various and sometimes free software tools.
The same is true when trying to erase data and files from a (low-end or high-end) live server. Most server operating systems are based on the same fundamental principle - deleting a file by using the server´s operating system tools is not enough. You have to securely erase it by overwriting the exact storage space where it was stored with special erasure tools.
Real-life scenarios
Imagine a data center for a large cloud service provider that has to delete several virtual servers or databases for a former client, while the physical server is still running and storing other applications. In this situation, securely erasing data from one client without affecting the functionality of the server, as well as the remaining applications and data from the other clients, is essential.
Another case where data must be securely erased from a working and live server is when a pilot project has come to an end. Imagine that your company wants to test SAP HANA as your new high-end and big data analyzing platform. Due to regulations and internal requirements, you can´t utilize the cloud version of this solution, so your only option is to work with a manufacturer to implement an on-premises test environment system. Since it makes no real sense to test this solution with fake data, you will use your own business-critical data to check if the system holds up to its promises. After several weeks or months of intensive testing and successfully analyzing your data, the testing is complete, but what happens with the data now? Your company most likely will not purchase the “old” test system, but instead, buy a brand new one. Additionally, the test SAP HANA will be used by other future clients, therefore, all of the business-critical data that was created during the pilot phase must be securely deleted before a third party acquires the same system. Just erasing the whole SAP HANA won't work since the system should be still working after the erasure process.
Other common cases where data should (and must) be securely erased from a live server may include employee data or old project data from research and development departments. Under the GDPR regulations, personal data from applicants and former employees have to be securely erased forever, failing to do so will result in large fines.
How is it done?
Erasing data from a live server is done with specialized data erasure tools. The leading product developer and vendor of these tools – Blancco – offers three different kinds of products to securely erase data from a live server – Blancco File Eraser, Blancco Removable Media Eraser, and Blancco LUN Eraser. As the name of these products suggests, each is specially developed to either erase files or complete LUNs in live severs with traditional hard drives. When it comes to servers that store their data on SSDs (NAND Flash Chips), Blancco Removable Media Eraser should be used, since the hidden spaces of the memory chip cannot be accessed by normal erasure tools. In any case, the responsible IT administrator or employee has to connect the laptop to the server with the appropriate Blancco software. After the software has scanned the file structure, it's up to the user to decide what files, folders, or LUNs need to be erased. How long the erasure process lasts depends on the size of the data.
There are certainly other products on the market which may be able to do the job, but the Blancco solutions are a great choice for companies managing large amounts of critical data. Each solution provides valid proof that data erasure has actually taken place, which is of enormous importance for regulatory and legal requirements.
Another solution to securely erasing data from a live server is to get help from specialists who can do this important job for you. Ontrack offers data destruction service for companies who want to be sure that their data is securely erased. Ontrack has all the necessary tools and knowledge to get the job done - and certify the successful outcome at the end.
Picture copyright: Manuel/pexels.com/CC0 License
Call for Immediate Assistance!
- Crypto Currency (2)
- Data Backup (9)
- Data Erasure (8)
- Data Loss (15)
- Data Protection (11)
- Data Recovery (22)
- Data Recovery Software (2)
- Data Security (3)
- Data Storage (15)
- Degaussing (1)
- Deleted Data (5)
- Digital Photo (2)
- Disaster Recovery (6)
- Encryption (1)
- Expert Articles (5)
- Hard Drive (7)
- Laptop/Desktop (7)
- Memory Card (5)
- Mobile Device (13)
- Ontrack PowerControls (1)
- Raid (5)
- Ransomware & Cyber Incident Response (6)
- Server (6)
- SSD (14)
- Tape (17)
- Virtual Environment (9)
