How to crack encrypted files
Encrypting your files is very important to ensure you keep your data safe, especially since the recent rise in ransomware attacks becoming more of an issue globally.
Even today, not only mathematicians and cryptologists but also hackers and criminals try to find new ways to “crack” encrypted documents. What happens if you need to crack encrypted files that you can no longer get access to? Find out below in Ontracks guide.
How to crack encryption
One of the most common ways to crack encryption is to test all the possible keys which nowadays is often with the help of computers can calculate hundreds of billions of keys per second – this method is called “brute force”. With the encryption method of Julius Caesar, for example, a person can quickly determine which key was used by testing. The simple approach: the letter “E” is statistically most frequently used, at least in English and German texts, so the exchanged letter should also occur most frequently in the encrypted text.
For longer keys, which are used nowadays, the required time to decrypt naturally increases so that computers are used to test the various possibilities by means of the “Brute Force” method and calculation.
Encryption types
In the First and Second World War the German military also strongly depended on the encryption of their orders. In addition to replacing one character with another character (substitution), the arrangement of the characters was also interchanged (transposition), for which a further key was required. This procedure, which was customary in the First World War, was, however, quickly cracked, as the Allies had excellent cryptoanalysts, who were only concerned with converting encrypted information into legible text. As a result, mechanical processes were developed and rotor cipher machines were built, with different substitutions being possible for each letter. The best-known of these machines was the Enigma used in the Second World War, which was considered uncrackable. However, it did not take long for this encryption method to be cracked by the enemy.
All previously mentioned methods use the same key for encryption and decryption, which is why these methods are called symmetric encryption. In the case of asymmetric encryption, which has existed for several decades, a completely different key (private key) is used for decryption than for encryption (public key). The secure network transmission paths “https” and “SSH” use these methods.
What affects the possibility of decryption?
In general, the longer the key the more difficult the decoding. The key length is measured in bits. The symmetric encryption algorithm, Data Encryption Standard (DES), which was considered not crackable until the end of the last millennium, used a 56-bit key, which means in order to crack with “Brute Force” 256 (= 72057594037927936) keys must be tried. In 1998 the “Deep Crack” computer, worth 250,000 US Dollars successfully cracked a 56 bit key for the first time in 56 hours. In 2006, the German universities of Bochum and Kiel combined efforts to build a computer that cost only 10,000 dollars, named COPACOBANA and was able to crack 56-bit keys in just 6 ½ days.
The successor to the DES encryption method is the “Advanced Encryption Standard (AES)” in versions AES-128, AES-192 and AES-256, whereas the numbers refer to the key length. AES-192 and AES-256 are approved in the US for state documents with the highest secrecy level and are currently not considered to be decryptable. However, this will not always be the case. In all codes generated by computers, a mathematical decryption solution can be found - at least theoretically. And with the “Brute Force” method it is only a question of the computing speed of the computer(s) used until one finally succeeds. In the case of AES you need a supercomputer, which would cost several billon US dollars. The estimated time to build the machine would take several decades.
There are, of course, a lot of other encryption methods currently used. But the methods used to crack the keys are the same: as long as there are no wanted or unintended backdoors or errors in the programming of the encryption and a mathematical solution has not yet been found, “violence” (brute force) must be used.
Can technology keep up with our decryption needs?
The NSA (one of the United States secret services organisations) which is the world leader in deciphering, is handling this problem pragmatically: if there is no way to “decrypt” databases a supercomputer is used to try the “Brute Force” method. If, however, it is clear that this does not help the problem is put on standby and left until the technology develops that will make the decryption feasible within a reasonable financial and temporal framework. If, however, it is clear that even this will not be successful, the problem is put on hold and left until the technology is ready so that decryption is feasible both financially and timewise.
Need help decrypting your files?
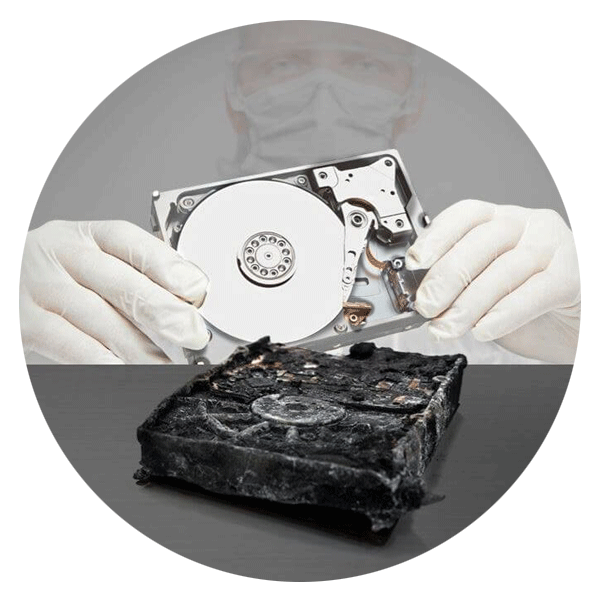
Our team here at Ontrack are data recovery experts, providing a superior service to customers who need help with their data storage and access. Contact us today to get help decrypting critical files you need access to again. We've completed over 600,000 recoveries so far, so you can be sure your data recovery is in safe hands.