Sharing Confidential Information over the Cloud
The risks associated with access to data for certain individuals, namely those who don’t need access to it, needs to be taken into account when sharing business data with other people within the same company, but not necessarily everyone, or with other partners and corporate clients, but not necessarily all of them. Confidential data sharing is not actually difficult, but the operating environment must be designed for it.
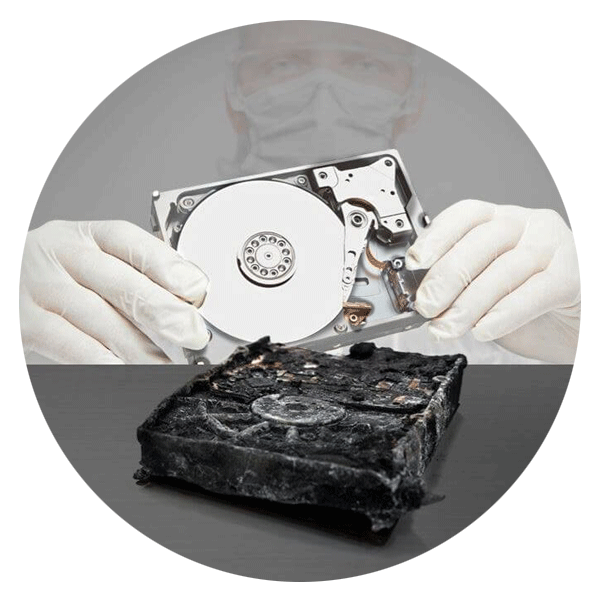
Anything that requires data sharing is a potential risk for the infrastructure that hosts them and the importance of the information within it. Addressing data sharing concerns data hosting and, therefore, a server which has the advantage of being designed to have a shared capacity to distribute information in many ways, and namely to the right person or group of people with a user account management that concerns access rights.
Reflecting upon this topic, we must being by thinking that about who needs access to the data and how much data needs to be shared? If it’s only within a company, there isn’t a problem of a bottleneck with the telecom lines, whose pricing is normally an obstacle. The introduction of services actually depends on the issue of access as confidential sharing is linked both to the concept of confidential access and to all court access. In order to access is from any line of any network, the access link is fundamental.
Moreover, it is difficult to control sharing in a global confidential corporate IT policy because the infrastructure has to be controlled by the IT department so that there are no unknown backdoors as unknown access is a risk. So, there are two main solutions. Either, confidential access is internal to the company and it’s only open to its internal network; therefore, it must not only be relatively confidential, but it must also encrypt content to ensure that no-one can find the location of the shared storage and read it. Or, confidential access is outside the company, in the Cloud, or hosted with a more conventional method.
In the second case which involves external hosting, data sharing is definitely most effective in the Cloud with a sophisticated data encryption, preferably with an encryption device that doesn’t depend on the Cloud hosting platform, so that you can have complete control over securing the encryption key. Another advantage of the Cloud is the ability to access it from anywhere, and access to all data types without monopolising the bandwidth of the telecommunications access link, as the case may be with external access to a company’s internal network. .
In any case, a pattern of sharing should be thought of in terms of who and how is using it as this is the basis of consideration so that no setting is forgotten.