How to protect your data on mobile devices – part one

The demand for the latest tech gives smartphone manufacturers a
great opportunity to frequently present new models to the market. People want a
sophisticated design and highly advanced technical specifications, and once
they have that, they want the next upgraded version!
The
evolution of these devices has been impressive. The first "non-smart"
mobile phone was a heavy, awkward device able to perform just the function of
the phone. Today, smartphones are powerful pocket computers, always connected
to the internet; much smaller, lighter and more easily transported than
laptops.
Digital storage that constantly grows and needs to be
protected
According
to Statista, 2019 saw 1.52 billion smartphones sold worldwide – a significant
increase from the 680 million units sold in 2012. The tablet market
continues to increase worldwide, but a report published by Analysys Mason states that sales have slowed down
considerably; with sales expected to fall to 129 million in 2022 from their
peak of 200 million in 2014.
Smartphones
are the most popular device used for accessing the internet, with Statista reporting close to half of those accessing the
internet in 2020 using a smartphone rather than a large format display.
But,
as users, do we realise and/or understand how much personal information we
store on our smartphones? And do we know how important it is to handle this
data very careful, especially when we decide to replace our device with a more
beautiful and powerful one?
Recycling and disposal: the market for reconditioned
devices
When
we choose to buy the latest smartphone, we often make the decision to give away or sell our old device,
since it is still fully functional.
Nowadays,
there are lots of people interested in getting second-hand smartphones and
tablets. There are some shops that buy them or offer trade-in deals upon the
launch of a new device. Most of these used devices, still in excellent
condition, will be technically tested to ensure they are in top shape and then
they will be resold as used: the idea is good, as it allows protecting the
environment and reducing the number of electronic waste.
The
market of the reconditioned mobile device is fast-growing. A survey conducted
by CCS, revealed a growing momentum for refurbished devices,
with 60% of UK respondents claiming they would consider buying a refurbished
mobile next time they change or upgrade.
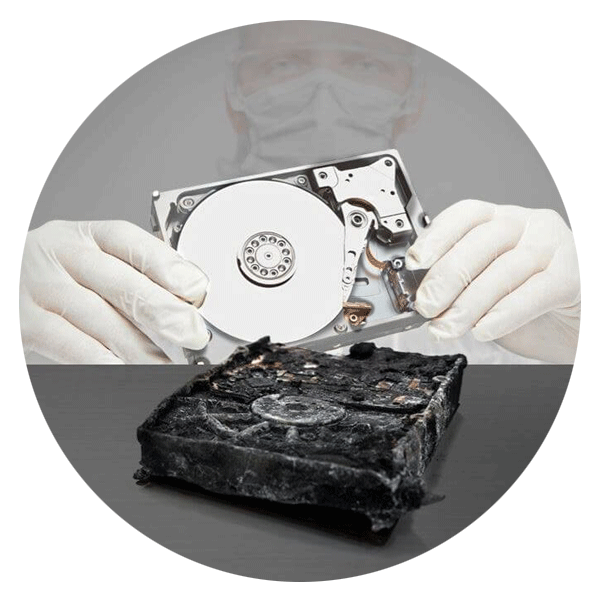
What data do we need to protect?
No
one would be happy to know that the buyer of their old device has unlimited
access to the data on their smartphone. Unfortunately, this is a reality for
some people who sell their old device without securely erasing the data that
resides on it. Not only could someone gain access to your photos, contacts,
emails, and files, but there is also a chance of losing control of our accounts
and passwords that could lead to fraud.
The
same applies to businesses. If a company fails to securely erase the data on a
mobile device assigned to an employee, which is then recycled or reused, there
is a chance of sensitive data getting into the wrong hands.
The
only way to protect ourselves and others is, therefore, to permanently
eliminate all traces of digital data. But what's the most effective method? In
the second part of this article, we discuss the erasure methods available, and
which is most effective.
Do you want to know more about how to protect your data throughout its lifecycle? Our latest report delves into the six stages of the data lifecycle and why it's so important to ensure you have an up-to-date strategy that protects data at each stage.
Download it here.