Safely incorporating BYOD into your workplace
One of the biggest trends in the tech sector at the moment is undoubtedly mobile. With smartphones and tablets becoming more powerful every year, many people now view them as a practical replacement for their desktop or laptop PC.
In the third quarter of 2015 alone, nearly 353 million smartphones were sold around the world - a 15.5 per cent increase over the same period the previous year, according to Gartner. And it is not only in people's personal lives where these devices are set to make an impact, as businesses across all sectors can expect to see these gadgets entering the workplace more frequently.
Often, business smartphones and tablets won't be issued by the company, but will be the personal devices of employees. This trend is known as bring your own device (BYOD), and if you haven't yet encountered it, you can expect to do so sooner rather than later.
There are many great benefits that can be seen as a result of embracing BYOD. It can provide a major boost to users' productivity by allowing them to work where and whenever they want, and it can also cut costs as firms do not have to invest in their own hardware. but it is not without its risks. In particular, securing these devices is a major challenge, as they give companies less control over their corporate data.
So how can businesses take full advantage of BYOD without leaving themselves exposed to problems such as data loss or hacking attacks? The UK government has published guidance on the issue, and it recommends a number of best practices that businesses should follow in order to stay safe.
Have an effective policy
One of the first things to do when implementing BYOD is to draft a clear, effective policy that spells out what staff members can and cannot do on their personal gadgets. This should start from a position of ensuring unauthorised devices cannot access sensitive data, then moving on to make sure only the data you are willing to share is available to employees.
It can be tempting to put highly restrictive policies in place to safeguard sensitive information. But if these are too strict, this will affect usability and encourage users to find their own workarounds - thus undermining the point of having a BYOD policy in the first place.
Get staff on board
A strong BYOD policy is worthless if staff don't understand it, or choose to ignore it. therefore, educating employees and getting their buy-in is vital to success. The government guidance notes: "Ensure that your staff understand their responsibilities when using their own devices for business purposes. This is important because many employees' approach to security will differ when using their own devices compared to using a corporately owned laptop or PC."
For example, they may be happy to share their own device with family or friends, or give it to a third party for repair, which may compromise sensitive data. Ensuring staff understand what they should and should not do with a device containing corporate data is therefore crucial.
Have contingency plans
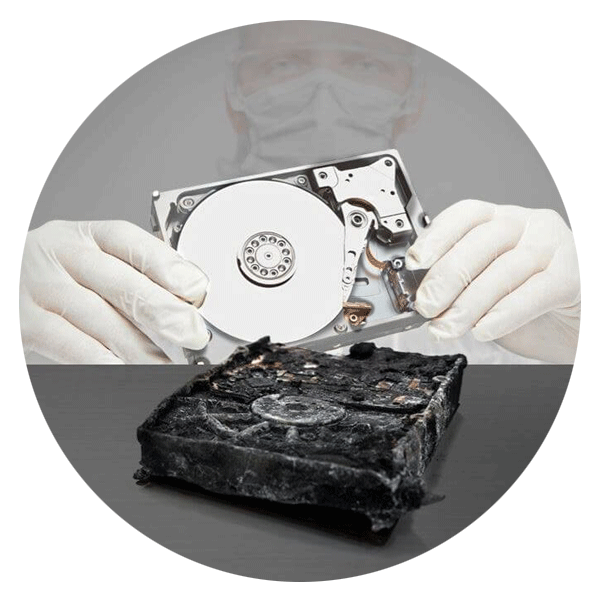
Where possible, information should not be stored locally on a user's device - and if it is, it should be automatically backed up elsewhere, for example by using cloud storage tools. If information is kept on a personally-owned smartphone or tablet that is lost or stolen, the ability to wipe the device remotely will be essential in order to prevent that data falling into the wrong hands.
Businesses need to expect that sooner or later, a BYOD gadget will be compromised. Therefore, they should have a plan in place for what to do in this eventuality. This should identify who in the organisation is responsible for managing a security incident and what actions will be taken to ensure data recovery.
"Staff must feel confident that they can quickly report incidents without fear of recriminations, especially if it's their own device," the guidance states.
Know the legal ramifications
When dealing with BYOD data, there will be a number of regulations that businesses will have to remain compliant. It's important to remember that responsibility for the information will still rest with the company's data controller and not the owner of the device. this means it's still subject to all the same rules as digital assets stored within a firm's network.
These include the Data Protection Act and the Employment Practices Code, which states that employees are entitled to a degree of privacy in the work environment. Therefore, companies need to tread carefully when managing devices which contain both corporate and personal data.
Consider alternatives
The more open businesses are about their BYOD policies, the more risk they open themselves up to. As the number of authorised devices using different platforms grows, along with the amount of data they can access, managing all this effectively can become a major headache.
However, there are alternatives to fully open BYOD. For instance, so-called 'choose your own device' is attracting more attention. While this is similar to BYOD, staff may only use one of a selection of pre-approved gadgets that the company can manage. 'Corporate owned, personally enabled' models, where the company buys the device but allows the employee to use if for their personal tasks as well, are another option that can offer more security.
Whatever the mobile model, organisations should be aware of the risk of business data being shared via personal applications and the company being exposed to attack from compromised apps.