Encryption – the oldest (?) discipline in the world
Contrary to what might be expected, information safety is as old as humanity itself. Before encryption, even the first primates to develop the ability to speak must have realized how important it was to keep a secret, as they would lower their voice to a whisper or communicate using signals shared only by the initiated. Secrecy became more of a serious matter once people had acquired the skill of writing –books or letters with important and confidential information had to be secured against the prying eye of an unauthorized audience. With this end in mind, sophisticated ciphers and enigmatic symbols were invented. They were understood only by those in the know. Be that as it may, first ciphers had to be relatively easy to understand, since encrypting and decrypting were performed by human, and thus the necessity of adjusting tools to the limited human capabilities.
Characteristic of that era was the types of ciphers popular then, such as substitutional (every sign replaced with another, following a specific pattern), transpositional (sequence of symbols in the encrypted text rearranged, also following a specific pattern) and their derivatives could have successfully been decrypted by linguists, although they were mathematical algorithms. In fact, if we take a closer look at a message encrypted in this manner, it turns out that in its structure it retains features of the source language. Assuming that a particular letter is used the most frequently (for instance, in Polish it is "A"), it is sufficient to find the most frequently used symbol of the cryptogram and replace it with exactly that letter. Using this strenuous, yet effective, method, one can decipher any passage.
Let us take Gaderypoluki (GA-DE-RY-PO-LU-KI) for an example. It is a simple cipher used by Polish scouts in which letters grouped into punctuated pairs are substituted with each other. As a result, every single letter A stands for G and the other way around, G for A, etc. The letters not included in the key remain the same. Below, we have encrypted the name of our company:
Iypuu Pntygci Opusig
Development of technology, especially in the field of military science, forced us to pick brains of mathematicians and engineers. Probably the most famous cipher machine – the German Enigma – used the substitutional cipher technique. Every sign would be independently encrypted by 26 discs, which made it the most efficient cipher machine in the world. After many years of work, to be exact in 1932, the Polish engineers had managed to crack the Enigma code. In the years to come, they mastered their technique to the point when intercepting German communications would take them less than a quarter. Interestingly, the Poles could do it despite the Germans incessantly changing their encryption methods and further complicating the code. The engineers created a cryptologic bomb which consisted of six Polish Enigma machines integrated with one another to break German ciphers.
New age of encryption
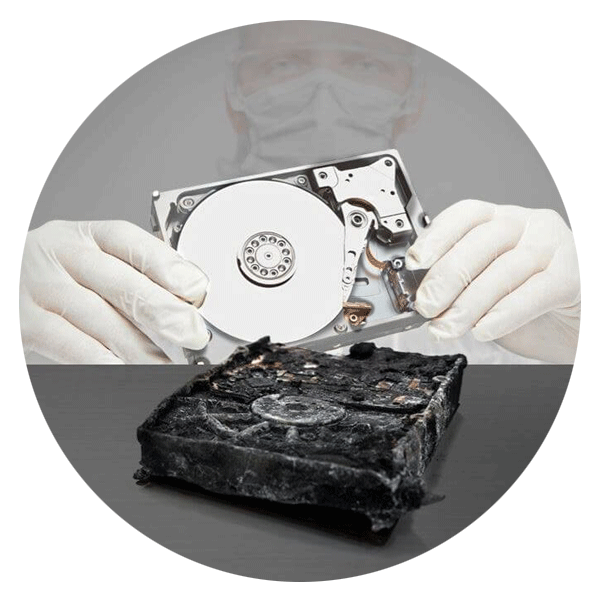
The invention of computers has forever changed the cryptological landscape. State-of-the-art computers process information more quickly than man. Breaking traditional ciphers is as easy for them as ABC – they do it within a split second, which renders old ciphers useless. The new age of cryptography has begun. It is no longer just a domain of the army and politicians. No, it is also a very important IT process used by everyone on a daily basis. Today, it is data storage devices that serve as books, while confidential letters have been replaced by other channels of communication, namely phone calls, text messages, e-mails and Internet payments, or even visits at trusted websites. All of the above ought to be efficiently ciphered as it is information criminals would be more than willing to lay their hands on. Hard drives in our computers store sensitive data, whereas our entire e-identity, as its name indicates, belongs to the e-world.
Modern encryption systems, more often than not, use asymmetric-key algorithms based on two keys: public and private. The first one encrypts information, the second one – decrypts it. In symmetric-key algorithms, which are rather unsafe, both keys can be derived from each other, that is to say using one will allow reading the other, if the mathematical operation is reversed. On the other hand, in asymmetric-key algorithms, even though deriving the public key from the private one is a relatively straightforward process, the reversal of this operation is very complicated and time-consuming, and in practice unfeasible with modern-day resources. The two most popular and frequently used encryption algorithms, RSA and DES, are based on this mechanism.
On the hard drive level, the computer can be secured through end-to-end encryption, which consists in encoding every single byte of data stored on the drive. This type of encryption can be programmed by system tools, dedicated equipment, for instance, Trusted Platform Module, a microprocessor-based system intended for encryption, or by use of special encryption software.To secure information stored on the computer, we can also use the encryption on the file system level. Both these protective measures complete each other and only by applying them parallelly do we secure important data. As end-to-end encryption of the hard drive only blocks unauthorized access to the drive, one's authorization relies on the verification of his access rights, most likely by typing in his login and password to decipher all data. So when the computer is on, data is not secure at all. It stems from the simple fact that in the case of end-to-end encryption one key is used for encrypting all information. The provision of this key deciphers it entirely without an exception. In consequence, the most important and sensitive information should still be encrypted from the file system level, which enables ciphering specific files and folders. In addition, encryption can be performed every time with another key; it significantly increases the safety of data.
Quantum computer – new cryptologic bomb
Modern-day methods of encryption provide unlimited safety. Attempts at breaking them would prove fruitless or simply economically too demanding for criminals. Even when using some supercomputer, cracking such codes would take ages. Be that as it may, as the technological breakthrough of inventing first computers had rendered old ciphers useless, so may the state-of-the-art cryptological technologies become insufficient to meet our future needs for encryption. Here, the quantum computer comes to the forefront, which would be another cryptologic bomb. Man may not be able to create a fully functional model of such a computer now, but much progress has been made in this field. One of the first such machines D-Wave, in which case scientists are not entirely sure, if it is an actual quantum computer in the classical sense, and these are mainly academic ruminations, is thousand times faster than traditional computers. It is still too little to break modern codes within a reasonable amount of time, but given the pace at which technology develops, another breakthrough could be a matter of time.
How is the encryption of data related to its retrieval? Unfortunately, encrypted data is very difficult to retrieve, like when we lose our key or when the authorization device breaks. As one of Ontrack experts notes, "data retrieval from an encrypted drive is reminiscent of putting together a puzzle of pieces that have the same shape and color."
Call for Immediate Assistance!
- Crypto Currency (2)
- Data Backup (9)
- Data Erasure (8)
- Data Loss (15)
- Data Protection (11)
- Data Recovery (22)
- Data Recovery Software (2)
- Data Security (3)
- Data Storage (15)
- Degaussing (1)
- Deleted Data (5)
- Digital Photo (2)
- Disaster Recovery (6)
- Encryption (1)
- Expert Articles (5)
- Hard Drive (7)
- Laptop/Desktop (7)
- Memory Card (5)
- Mobile Device (13)
- Ontrack PowerControls (1)
- Raid (5)
- Ransomware & Cyber Incident Response (6)
- Server (6)
- SSD (14)
- Tape (17)
- Virtual Environment (9)
