Understanding GDPR Article 17 and the Need for Secure Data Erasure

What sounds easy and has already happened accidentally without any further action, can be difficult to implement in reality. For one thing, you have to know what exactly should be forgotten. On the other hand, you have to know how to actually forget everything completely. Without just a spark of information, the pink elephant can still be found.
To find that out, you have to go deeper into the subject of data protection.
For example, have you ever wondered while standing in line at the checkout counter about the telephone number that you have to give the clerk along with your payment? What is this number be needed for? Where does this number end up? And what ultimately happens with it?
These questions will become explosive towards the end of May when GDPR is finally implemented and threats of high penalties for companies that deal too loosely with the personal data of their customers, partners, or other contacts. For example, with GDPR Article 17 of the European Data Protection General Regulation, the existing German data protection law, which is already quite strict in comparison to the other laws of the European partner states, was again tightened by the new law. Especially so that those affected can now claim the "right to be forgotten" of their personal data.
In short, GDPR Article 17 ensures that companies must immediately delete personal data if the following occurs:
- The personal data are no longer necessary for the purposes for which they were previously collected or otherwise processed
- The person withdraws their consent and there is no other legal basis for processing
- The data subject objects to the processing and there are no legitimate grounds for processing
- The personal data have been improperly processed
- The deletion of personal data is required to fulfill a legal obligation under European Union or national law
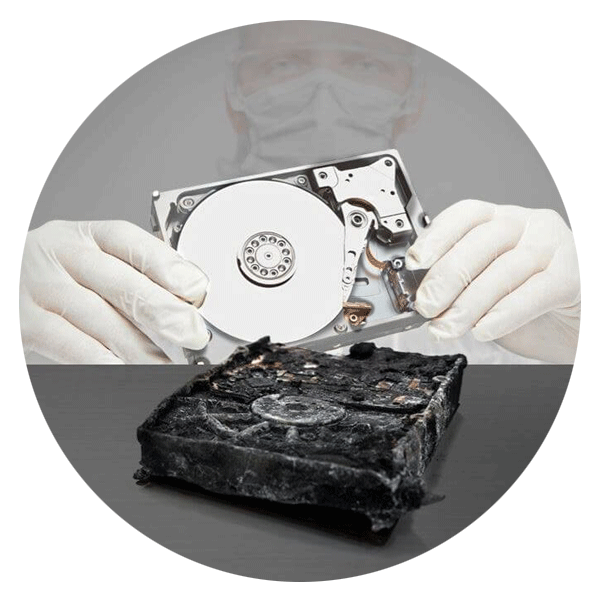
In one of these cases, it's not enough to simply throw a USB stick that contains personal information in the trash. It must follow the legally established and appropriate deletion processes if the device is to be reused.
Many companies use data from their customers and affiliates for different reasons and different departments stored this data in their systems in the past, diligently merged from system A into system B or even connected system A to system B for practicability. Lieschen Müller and her telephone number became Lisel Mueller or Liese Müller with and without a telephone number. And who tells us that there is not more than one Lieschen Müller?
First of all, it should be clarified what the personal data of the data subject are, where, when, and under what circumstances which data was collected. After that you have to be clear about where these data were saved and stored.
If you had an overview here, you would have to clarify what has to be forgotten. Is this data still needed? If so, which department still needs this data? If so, where and for how long may I retain the required data? And what if this data has already been submitted to a third party or even the general public? Again, the responsible body is obliged as far as possible to ensure the deletion.
If these questions have been completely clarified, a secure deletion of the data has to be done. Surprisingly, the pink elephant has stuck its trunk in many departments and left more or less profound footprints in many places. Thus, their legacies can be found not only in the folder for received messages, but also after deletion in the folder for deleted messages. If one deletes the data from the one database, then they suddenly emerge as backup data, happily blushing, to another place or are only deleted as a partial data record from dependent systems and, in the worst case, leave a pile of broken pieces in the dependent system.
According to GDPR Article 17 DSGVO, the deletion has to be done immediately after the request, it is advisable to prepare for these requests early on and to have ready a safe deletion software, which can be used and used fast, efficiently and across all systems.
If you're in need of data erasure, click here for more information regarding Ontrack's secure data erasure solutions.
Call for Immediate Assistance!
- Crypto Currency (2)
- Data Backup (9)
- Data Erasure (8)
- Data Loss (15)
- Data Protection (11)
- Data Recovery (22)
- Data Recovery Software (2)
- Data Security (3)
- Data Storage (15)
- Degaussing (1)
- Deleted Data (5)
- Digital Photo (2)
- Disaster Recovery (6)
- Encryption (1)
- Expert Articles (5)
- Hard Drive (7)
- Laptop/Desktop (7)
- Memory Card (5)
- Mobile Device (13)
- Ontrack PowerControls (1)
- Raid (5)
- Ransomware & Cyber Incident Response (6)
- Server (6)
- SSD (14)
- Tape (17)
- Virtual Environment (9)
